From Claude with some prompting
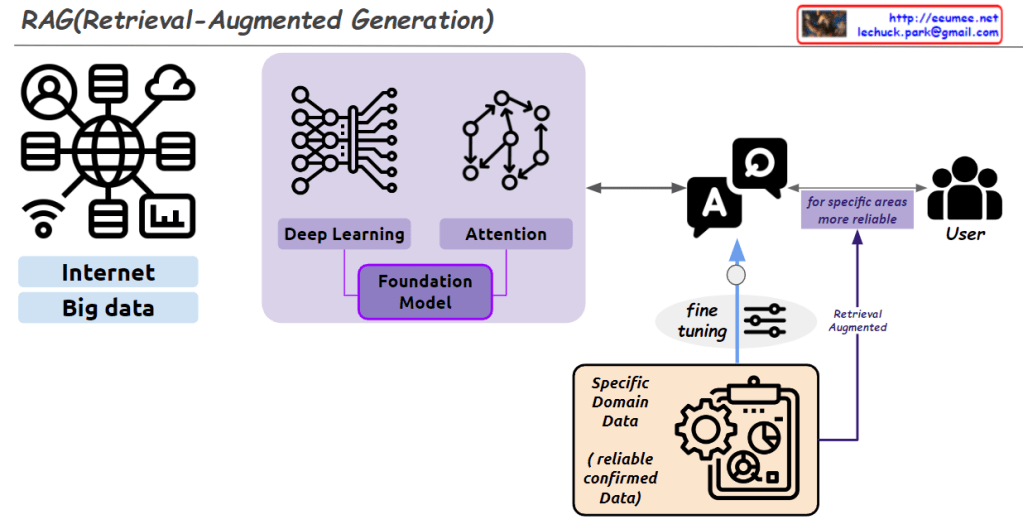
This image explains the concept and structure of the RAG (Retrieval-Augmented Generation) model.
First, a large amount of data is collected from the “Internet” and “Big Data” to train a Foundation Model. This model utilizes Deep Learning and Attention mechanisms.
Next, the Foundation Model is fine-tuned using reliable and confirmed data from a Specific Domain (Specific Domain Data). This process creates a model specialized for that particular domain.
Ultimately, this allows the model to provide more reliable responses to users in that specific area. The overall process is summarized by the concept of Retrieval-Augmented Generation.
The image visually represents the components of the RAG model and the flow of data through the system effectively.