From Claude with some prompting
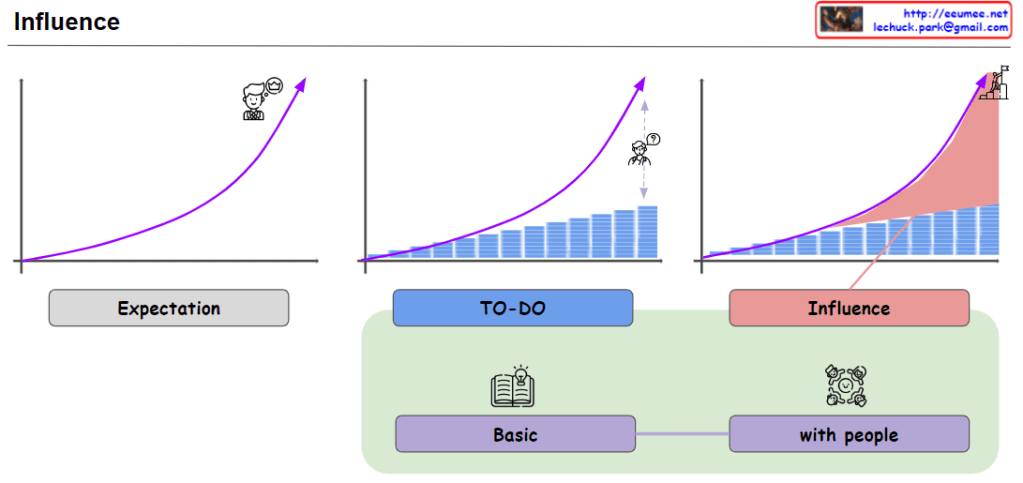
This image illustrates the process of achieving an exponential expectation or goal for a particular endeavor.
- The “Expectation” graph shows an exponential rise, representing the ambitious target or desired outcome for the endeavor.
- To reach this expectation, one must first go through the “Basic” stage of steadily growing and developing individually, step by step.
- Then, in the “with people” stage, one needs to expand their influence by collaborating and interacting with others, leveraging interpersonal relationships.
- The “To-Do” graph depicts the accumulation of basic tasks and responsibilities in the individual growth stage.
- Ultimately, the exponential expectation can only be achieved through a combination of consistent personal growth at the basic level, coupled with an expansion of influence via relationships and interactions with others.
In summary, the image emphasizes that to attain ambitious, exponential goals, consistent individual effort must be complemented by leveraging a broad network of interpersonal connections to amplify one’s influence and impact.