
2024 New Year

The Computing for the Fair Human Life.

From DALL-E with some prompting
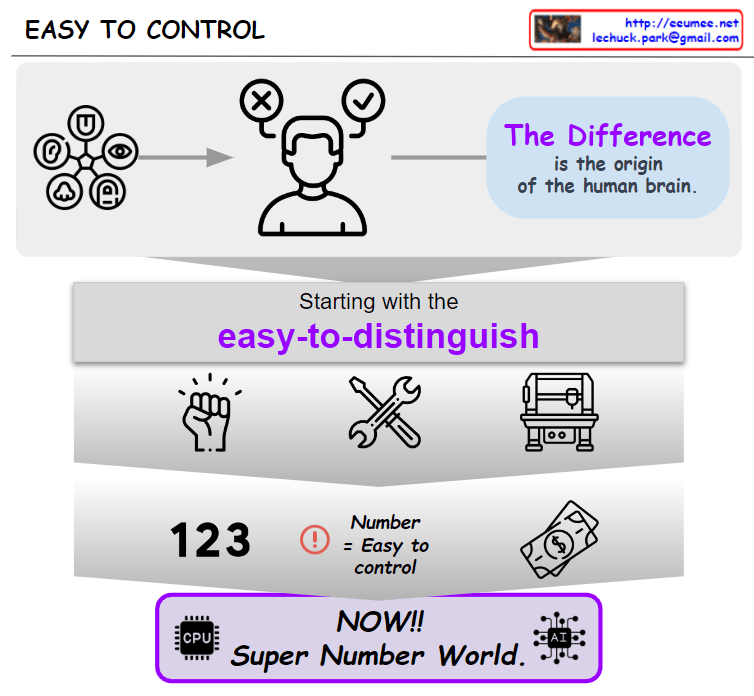
This image represents the connection between human discernment and numeric-based control systems. Humans possess the ability to detect and understand complex differences, which is crucial for the advancement of capital and business. Starting with simple and distinguishable elements, we have evolved to represent and control increasingly complex economic systems through numbers. The ‘Super Number World’ symbolically represents how we utilize technology, especially computing and artificial intelligence, to manage this complexity. Ultimately, the growth of capital and business is represented and understood through numbers, and controlling these numbers creates the most significant differences in the modern economy.

from DALL-E with some prompting
The image represents a diagram that outlines the transformation of data center operations through the integration of Artificial Intelligence (AI). The flow from left to right demonstrates the transition from traditional data center operations to a new paradigm facilitated by AI. The diagram begins with legacy operations characterized by machines, alarm systems, and the processes managed by experts.
The section titled ‘DC Growing’ highlights the expansion of data centers and the new challenges that arise, including hyperscale, increased complexity, and shifts in customer demographics from retail to major Cloud Service Providers (CSP).
In the subsequent ‘DT’ and ‘AI’ sections, the diagram showcases how Digital Transformation (DT) and AI are integrated into data center operations, enhancing service reliability, automation, energy optimization, and customer service. The ‘AI Accelerator’ section illustrates the role of AI in speeding up the operations of a data center, setting new benchmarks for AI-driven operations.
This diagram visually summarizes how data centers evolve with technological advancements and how AI and digital transformation technologies are revolutionizing traditional operational practices.

From DALL-E with some prompting
This image seems to describe the concept of a software system. It emphasizes that the system should not only operate mechanically but must also integrate and understand expert knowledge and human processes through digitalization.
At the top of the diagram, there are images of a computer labeled ‘Just System’ and an expert labeled ‘Expert,’ suggesting that traditionally, systems and human experts operate separately.
In the center, within a large framework labeled ‘Digitalization,’ the ‘System’ and ‘Expert’ are interconnected. This represents the need for systems to understand how machines and systems work and what is desired during the digitalization process.
At the bottom of the diagram, the phrase ‘It’s not just system. All works by systems. So, System must understand real works.’ highlights that the system is more than just mechanical operation; all work is done through systems, and therefore, the system must understand the actual work.
From DALL-E with some prompting
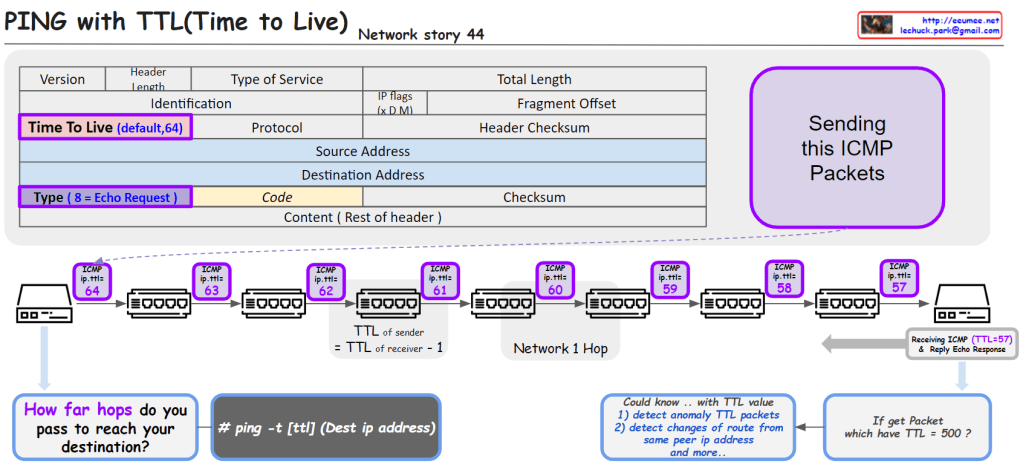
The image provides an educational visualization of how the “Time to Live” (TTL) value in the Internet Protocol (IP) is used to manage the life span of data packets during transmission. TTL is a crucial part of the IP header, which is decremented by each router the packet passes through. When the TTL value reaches zero, the packet is discarded, preventing it from circulating indefinitely.
The diagram outlines the following key points:
# ping -t [ttl] (Dest ip address) that specifies how to ping with a defined TTL value.This visual aid is likely used for educational purposes to teach about network packet management, routing, and network troubleshooting techniques.

But we are not..

From DALL-E with some prompting
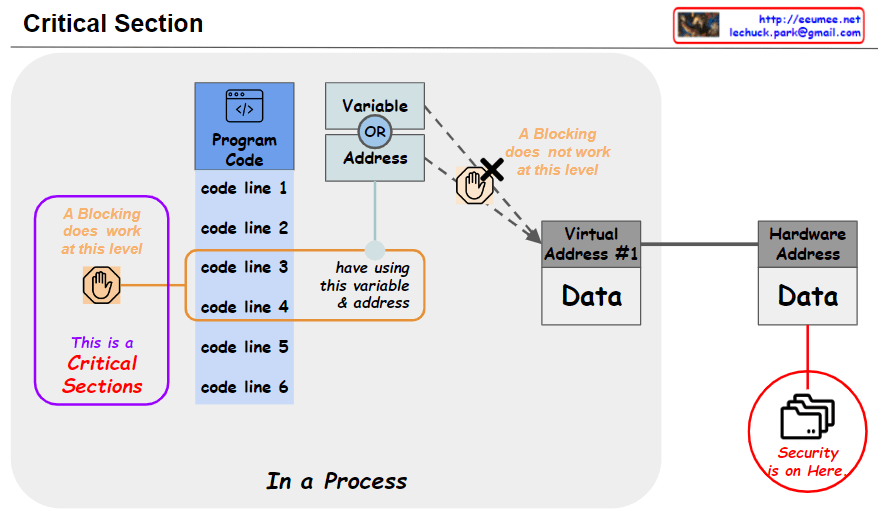
The provided image delineates the concept of a “Critical Section” in process execution, where certain areas of the program code are designated as sensitive or exclusive zones to prevent concurrent access. This is not merely a matter of securing a memory location but rather about managing access to specific code blocks that interact with shared variables or addresses.
In the diagram, the “Critical Sections” are highlighted to signify that these blocks of code are where ‘blocking’ occurs, allowing only one thread or process to operate on the shared resources at a time, thus ensuring data integrity and preventing race conditions. The transition from code lines to data, through variable addresses and virtual address mapping to the actual data in hardware, suggests a layered approach to security and access control.
Moreover, the image hints at the abstraction layers from a virtual address space to the physical hardware address, underlining the importance of security protocols at each layer. These critical sections act as a checkpoint not only to enforce sequential access to shared resources but also to facilitate a systematic flow of operations, from programming syntax to system calls, and from understanding the computer architecture to the actual hardware operations. This systematic control is crucial for maintaining security and operational efficiency in digital systems.