From Claude with some prompting
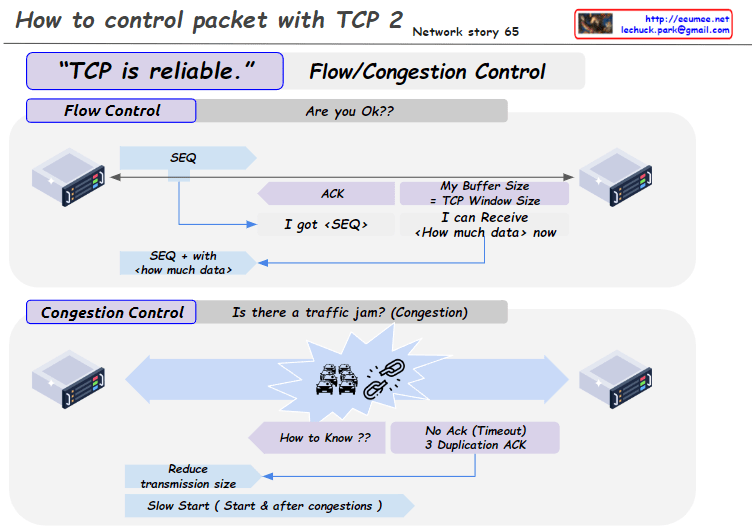
This image is a diagram explaining the TCP Congestion Control mechanisms, particularly comparing the congestion control algorithms of two TCP versions: Tahoe and Reno.
Key points:
- Both algorithms use a Slow Start Threshold (ssthresh) to determine the initial congestion window size.
- The congestion window grows exponentially (2^n) at first, then switches to linear growth (+1) once it reaches ssthresh.
- Both algorithms reduce the congestion window to 1 and adjust ssthresh to half of the current size upon a timeout.
- When receiving 3 duplicate ACKs (3 DUP ACK), both algorithms halve their ssthresh.
Difference:
- On 3 DUP ACK:
- Tahoe: Reduces congestion window to 1
- Reno: Multiplicatively decreases congestion window
There doesn’t appear to be any incorrect information in this image. It accurately shows the key difference between Tahoe and Reno in their response to 3 DUP ACK situations, and correctly explains other aspects of congestion control as well.