From DALL-E with some prompting
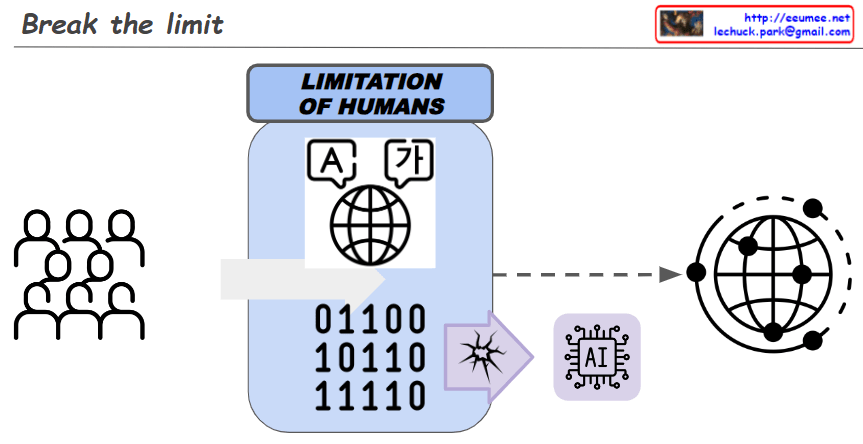
This image illustrates how AI transcends human limitations in accessing reality, which includes everything in the universe, through language or numbers, allowing for a more direct approach to the actual substance. On the left, a box labeled ‘LIMITATION OF HUMANS’ contains mathematical symbols, a globe, and binary numbers, symbolizing the complexities of calculation, global comprehension, and data processing that are human constraints. In the center, an obstacle is shattered, depicting AI breaking through these limitations and connecting more profoundly with the real environment on the right. Accompanied by the text “Break the limit,” it suggests the boundless potential of AI to reach an intrinsic understanding of reality.