From Claude with some prompting
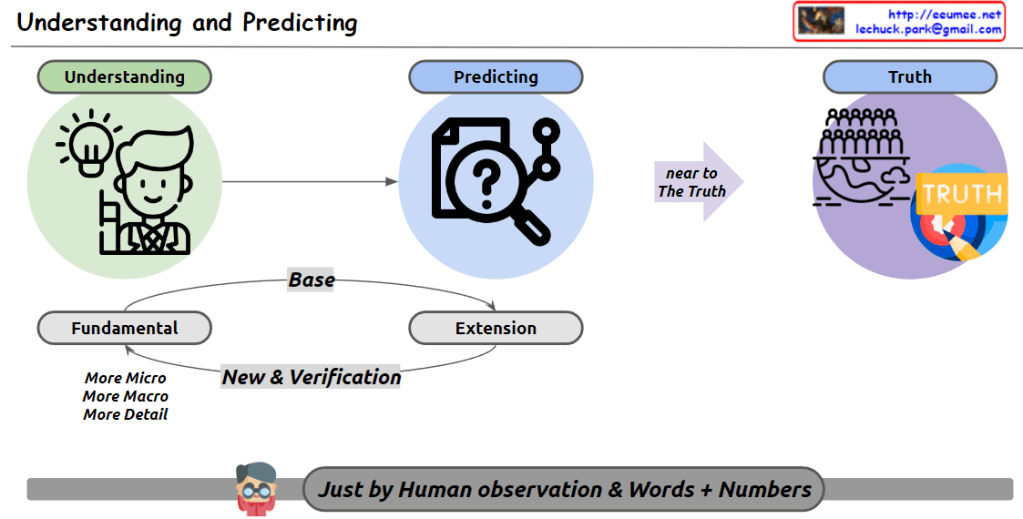
This image illustrates the human process of approaching truth through understanding and prediction. The key components are:
- Understanding: Represented by a lightbulb and a human icon, signifying the acquisition of basic knowledge.
- Predicting: Symbolized by a magnifying glass with a question mark, indicating the stage where understanding is used to make predictions.
- Truth: Depicted by a group of people and a “TRUTH” label, representing the ultimate goal.
These elements are connected sequentially, with prediction aiming to get “near to the Truth.”
The process is built on two foundational concepts:
- Fundamental
- Extension
These concepts interact through “New & Verification,” with the fundamental aspect encompassing “More Micro, More Macro, More Detail.”
Key Insights:
- Continuous Approach to Truth: Humans are constantly moving towards truth through understanding and prediction. This is a dynamic process, not a static one.
- Knowledge Expansion and Refinement: We expand our knowledge by exploring fundamental concepts more microscopically, macroscopically, and in greater detail. This represents growth in both depth and breadth of human knowledge.
- Limitations of Human Perception: The phrase “Just by Human observation & Words” at the bottom of the image highlights a fundamental limitation. We can only understand and express the world through our observations and language, not through direct access to matter itself.
- Role and Limitations of Numbers: While mathematical expressions can help overcome some linguistic limitations, they too face boundaries when confronting the infinite complexity of the microscopic and macroscopic worlds.
- Infinite Nature of Knowledge: As we learn more, we discover there is even more to learn. This paradox suggests an endless journey of discovery and understanding.
- Dynamic Process: The pursuit of knowledge is ongoing and ever-evolving, constantly expanding and becoming more refined.
In conclusion, this image portrays the continuous human quest for knowledge and truth, acknowledging our perceptual and expressive limitations while emphasizing our persistent efforts to expand and deepen our understanding of the world around us.